“The Keyboard Doesn’t Lie”: A Conversation with Army Veteran Hacker, and Entrepreneur: Tyrone E. Wilson

“You should ask yourself 3 question: What do you love doing? What are you good at? And what does the world need? If you love it, your passion for it will shine through. If you’re good at it, it will come easy to you. And if it’s what the world needs, there will be demand for it.”
From securing military networks as a soldier in the US Army, to building his own cybersecurity company, Tyrone E. Wilson recently joined us on the podcast to chat about his InfoSec journey. In this conversation, we explore a number of topics, including a formula for discovering your ‘dream job’, the skills veterans bring to the security industry, and how to combat the perception of ‘what a hacker should look like’. Tyrone also shares a free resource you can use to build your own Security Operations Center (SOC) and brush up on skills, such as threat hunting, intrusion detection, network security monitoring, and more – for free.
Listen to the full episode here.
AI is everywhere. Cybersecurity is no exception. Security professionals looking to prepare themselves for the technology of today and beyond have a responsibility to understand artificial intelligence: how it works, what it can do, and perhaps most importantly: how it breaks. Companies including TCM Security, CompTIA, OffSec, ISACA, and SISA have you covered with their new lineup of AI Cybersecurity Certifications.
The Wallarm API Security Level 1 certification is a free, hands-on program designed to bridge the gap between theoretical security and real-world defense.
SquareX Field CISO John Carse interviews Gautam Sharma on the ‘Be Fearless’ Podcast about thoughts on hacking AI, browser security, workforce challenges, and concerns around academia regarding cybersecurity education.
When it comes to cybersecurity education, there are several specific reasons that universities are struggling to prepare students for the demands of the workforce.
Artificial intelligence (AI) is doing exactly what security teams hoped it would do: eliminate the repetitive, low-value work that has long burned out junior analysts. But in solving this problem, it may be creating another one that could have a long-lasting impact.
In many organizations, the next generation of cybersecurity experts is already in the building. IT, compliance and operations staff often have the foundational knowledge to transition into security roles with the right support. Yet, companies frequently default to external hiring, overlooking people who already understand their systems, data and culture.
Check out these Black Friday and Cyber Monday (2024) deals on your favorite cybersecurity / infosec gear and training, including TCM Security, hak5, Protonmail, and more.
“Despite its toy-like looks, this pocket-friendly multitool can be used for all kinds of hacking and penetration testing. It gives anyone an easy way to interact with the invisible waves that surround us, whether they’re RFID, NFC, Bluetooth, wifi, or radio. Think of it as a hacker Swiss army knife that you can buy for less than… “Continue Reading on Lifehacker
C-Suite & Senior Cybersecurity Executives gathered at Cipriani’s on Wall Street to discuss emerging threats and solutions in cyberspace, as part of the Official Cybersecurity Summit.
Developers, engineering leaders, and technology infrastructure professionals met at City Winery in New York City as part of Unscripted — the modern software delivery conference, hosted by Harness
Cybersecurity professionals, investors, and entrepreneurs gathered at The Yard — a co-working space in Midtown — to hear HacWare Founder and CEO, Tiffany Ricks discuss her enrerpreneurial journey into the world of cybersecurity.
Hundreds of members of the cybersecurity community gathered at the Tampa Theater in Tampa, Florida to celebrate the national premiere of the Do We Belong Here documentary, produced by Cyber Florida, and based on the podcast of the same name. Do We Belong Here highlights the stories of women in cybersecurity, showcasing their challenges and triumphs.
Cybersecurity professionals and business leaders across New York City gathered at Convene in Midtown for HackerOne’s Security@ Conference. The event, which is part of a global tour, brought together security practitioners for an evening of networking, discussions.
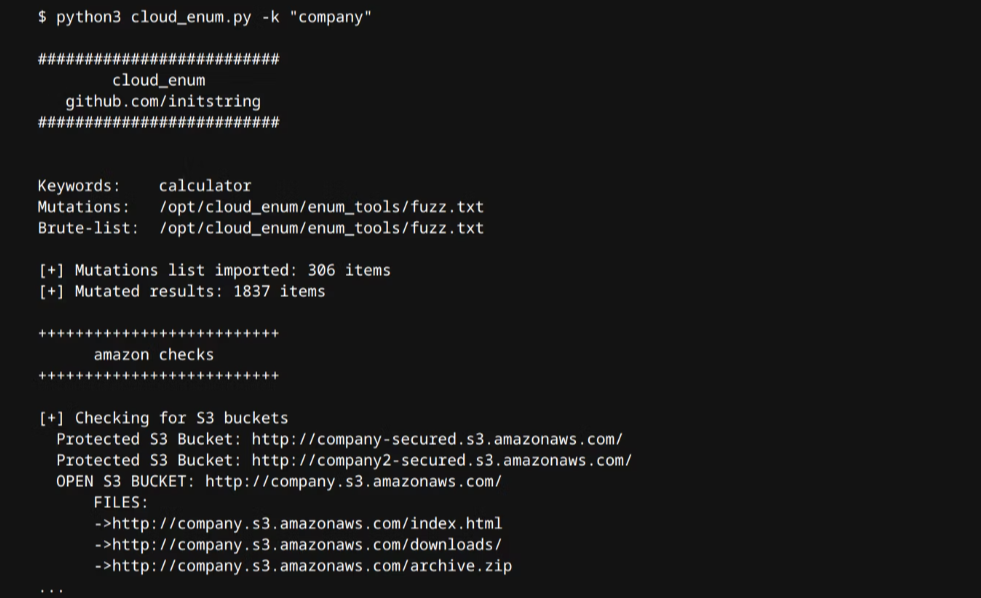
Want to get started as a security researcher and hunt bug bounties? This detailed guide by NOVASECIO, available on the bug bounty platform Intigriti, shows researchers how to discover misconfigured AWS Simple Storage Service (S3) buckets.
Thousands of cybersecurity enthusiasts recently gathered at the Metopolitan Pavilion in Chelsea for Cybertech NYC, which describes itself as 'The Main Forum for Technology Leaders and Investors in Cybersecurity & AI’.
Students and aspiring cybersecurity professionals often ask: “Do I need to know programming to work in cybersecurity?“ Here’s the answer.
Cybersecurity training organization, OffSec recently announced a new entry-level cybersecurity course and credential, the OffSec CyberCore Certification and its accompanying course, SEC-101: Cybersecurity Essentials. The course covers Windows and Linux basics, Python Scripting, Networking, Powershell, Data Transformation, as well as Frameworks and Standards, and other in-demand security related skills.
A recent article from an anonymous author, ‘Chadly McCyberton’, claims that cybersecurity jobs no longer exist, encourages job seekers to give up. We’re not okay with that.